WordPress has developed, in some circles, an unfair reputation for having security risks. Research has clearly shown that the WordPress platform is safe. But this may lead some people to ask, if the platform is so safe, why do WordPress sites get hacked?
In the majority of cases, it is because those responsible for the site failed to follow some very simple web safety protocols. Let’s take a look at five reasons why your WordPress site may be at risk of getting hacked and the steps you can take to prevent it.
Failure to Update Plug-Ins
In a multiyear tracking style by Hosting Canada, researcher Gary Stevens found that the most common cause of WordPress-related hacks were due to unupdated plugins. Plugins that have gone years without any updates offer a backdoor buffet for potential malicious third parties.
When you update WordPress plug-ins, you accomplish the following things:
- You increase security
- You fix bugs
- You add security features and functionality
You increase the security because you patch vulnerabilities, which strengthen your plug-ins against attack. Updating plug-ins might seem tedious, but, remember, hackers and malicious individuals are paying close attention release notes. When hackers learn about a vulnerability in a plug-in, they immediately start to exploit it. Keeping your plug-ins up-to-date reduces your site’s vulnerability.
2. Insecure Web Hosting
Web hosting has a larger impact on the security of your WordPress website than you might think. If you choose the wrong hosting, you may leave your site open to exploitation and unwanted downtime. This is especially true when discussing shared hosting. Shared hosting makes security a shared responsibility.
Many people opt to host to their WordPress site using shared hosting because it’s inexpensive. But this brings a number of security drawbacks. Shared hosting functions because multiple sites are using the same infrastructure. And this is where the problems start. Your site could become exploited by something that’s happening on another site, which shares your server, if directory permissions and file permissions are weak.
3. The Dangers of Using Weak Passwords
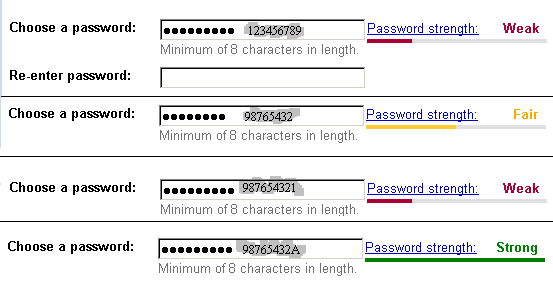
You have the responsibility to ensure that your WordPress website is secure by choosing effective passwords. WordPress offers passwords for a reason. Brute force attacks are designed to take advantage of weak passwords. There are number of steps you can take to improve the strength of your WordPress password.
- Follow the recommendations offered by WordPress. WordPress recommends that your password be at least six characters long, that it includes upper and lowercase letters, and that it includes numbers and symbols. This might sound like a simple recommendation, but the truth is that the more complicated your password is, the harder it will be for someone to break through.
- Longer passwords are better. Although WordPress recommends a minimum of six characters, you want your password to be as uncrackable as possible. Make it between 10 to 50 characters. Longer passwords are associated with increased password entropy.
- Keep your password random. Complexity is a key aspect of WordPress password security. A random combination of alphanumeric characters that includes random symbols is one of the best defenses against cracking. Using word combinations from the dictionary makes it easier for hackers to guess your WordPress password.
- Do not reuse passwords. It’s easy to think that reusing a password from a few years ago is safe. The danger lies in the fact that you may have used this same password a few years ago on another site that has been compromised and linked to you.
- Use two factor authentication. Two factor authentication adds an additional layer of security to your account. When you enable two factor authentication on WordPress.com, you will be required to input a pass code that has been randomly generated and sent to your mobile device.
4. Weak Username
By default, WordPress gives you the username admin. If you do not change this default username, you are doing half of the work for the hackers. In order for them to hack your WordPress account, they need to be able to decipher your username and your password. One of the first things that they are going to do is attempt to gain access by using the username admin.
It is also recommended that you avoid using your common email address as the username. You would also want to avoid things that are easily associated to you, such as your name or a combination of your first name and the first letter of your last name. Although you do not need to keep your username as complicated as your password, you definitely do not want your username to be something that a hacker can easily guess.
Another mistake would be checking the box for keeping you logged in if you are on a computer that is used by a number of people. If you do, you are exposing your username and taking away a level of security that can protect your site.
5. Change WordPress Table Prefix
Anyone who has ever done anything with WordPress understands that WP_ is the prefix for tables created by WordPress by default. Most people do not change this because they either do not know that the option exists to make this change or do they do not see the importance of doing it. You get the option to change the prefix during installation.
We recommend that you use a prefix that is a little bit more complicated. This is to make it more of a challenge for hackers to guess your database table names.
WordPress is one of the most popular platforms for creating websites today. As WordPress continues to expand its functionality, we should only expect it to become more and more popular. With popularity comes unwanted attention from people looking to exploit its vulnerabilities. By following the five steps mentioned above, you can go a long way in keeping your WordPress site secure.
Are there some other tips that you have followed to successfully secure your WordPress site? We would love to hear from you. Tell us about them in the comments section below.